UQ Students should read the Disclaimer & Warning
Note: This page dates from 2005, and is kept for historical purposes.
COMP3502 – Assignment One – Trusted Computing
Specification | Marking Scheme | My Submission | My Results
You have just graduated, and been employed by “Business Communications Consulting” as an IT expert. Your boss, Director of Technical Systems, has been asked to provide the board of directors with a report about the Trusted Computing Platform Alliance, so that the board can determine whether there are any implications for its strategic plan. Your boss is too busy to do it himself, and delegates the task to you. He gives you the following guidance:
Find information about the Trusted Computing Platform Alliance, including
- the assets it will protect;
- the threats that it addresses;
- the mechanism that is to be used, and briefly how it works;
- how well the mechanism will counter the threat;
- how much the mechanisms could frustrate legitimate users; and
- possible ethical, social, economic and/or political effects.
Make sure you use at least three different sources of information, and around 1500 words should be enough for the level of detail I’m after.
As you are keen to demonstrate your critical judgement and communications skills to your new employer, you will include an appendix (no more than 600 words) that describes how you have evaluated your different information sources:
- Describe how you judge how objective and authoritative an information source might be. (You will need to provide at least one or two references for your “critical thinking” sources here.)
- Describe what “peer reviewed” means in the context of the scientific literature, and comment on what this might mean for readers of that literature.
- Give examples of TCPA information that may be misleading, deceptive, or biased, and explain why you think this may be the case.
- Give an example in which one source would classify something as a threat, where another source would classify the same thing as legitimate use. Decide whether there is a single “correct” truth, or give examples of different points of view where each one may be correct.
Notes:
At least one of the sources you use must have been through a “peer-reviewed” process,
meaning that it is published in a scholarly journal or presented at an international (or international-quality) conference. Do not attempt to use Google to locate this sort of information: use library databases instead. Librarians will be very helpful, unless you are in a rush – talk to them early if you are not familiar with the databases.
You are required to describe a source that has a very low standard of objectivity and authority. It should be very easy to find one yourself using Google, but http://www.againsttcpa.com/what-is-tcpa.html is one example.
In the field of security, we are faced with attackers who may try to influence our behaviour (or our computers’ behaviour) for their own purposes. In some cases, this concept could be used to describe some of the information sources we may come across. It is important to be able to determine how appropriate (accurate, objective, unbiased, true) this information might be. Some students may not be used to criticising other written material, but that will be is necessary in this assignment. Criticisms should be objective and factual, and should themselves satisfy criteria you use to judge others.
When counting words, you should not include the executive summary (or abstract), references, appendices, or lengthy quotations.
There is no particular referencing format required, but the one you select should be applied accurately and consistently. The library can provide details for suitable schemes. As a reminder, there are marks allocated for references.
You should structure your report logically. You should use headings where they will help the reader. It is not necessary to structure your report strictly according to the details your boss asked for, although you may judge that to be appropriate.
The word count suggestion is not a “hard limit”. You can go over or under a little if necessary. However, be aware that communication skills are very important. If you were, for example, to submit a 5000 word assignment, you may be demonstrating an inability to follow instructions or an inability to communicate clearly and succinctly.
This is an individual assignment, not one to be done by groups. Locating information is an important skill that is assessed in this course. While it would be acceptable to give another student help in using the library databases, the actual task of finding, selecting, and judging individual information sources must be done by each student.
You are required to read information from a number of sources, understand a topic, and then formulate your own words to answer the particular questions asked above. Where you can find no better way to express an individual idea than the words used by one of your sources, you should enclose those words in quotation marks, and refer to their source. Anything less is plagiarism.
Students are reminded of the School’s policy on academic misconduct, which is available on the web site, and referenced in the course profile.
I hope that if you produce a good assignment, you will not object to having it published on the web site (your choice as to whether your name is included or not).
I do not want this assignment to be “guess what the teacher wants”. If you have questions about the assignment, look first at the course objectives, and then ask me questions either privately or in the newsgroup.
Students should not expect any assistance from the lecturer or tutors on this assessment in the last 4 days before it is due in.
Marking Scheme
Description of assets, threats, use, and misuse. (Demonstrate correct interpretation and application of security vocabulary, and adequate comprehension of literature. Demonstrate identification of frustration of legitimate use.) |
4 marks |
Brief description of mechanism(s) the system will use to counter the threats. (Has an adequate explanation of why the threat will no longer succeed, or be less likely to succeed.) |
3 marks |
Social, ethical, economic, political consequences. (Demonstrates an awareness of related social etc. issues, and provides a logical argument as to what effects this system may have, and why.) |
2 marks |
Information sources. Located at least one peer-reviewed & at least one poor-quality. You should use at least four independent sources on the TCPA, and at least one for critical thinking/web page evaluation. |
2 marks |
Referencing. (Reference list contains necessary information, chosen formatting is used consistently.) |
2 marks |
Criteria for evaluating sources identified and applied 3 marks |
3 marks |
Criticism of poor source 2 marks |
2 marks |
Report structure (logical flow) 2 marks |
2 marks |
My Submission
Trustworthy Computing
Introduction
Computers are fast becoming prevalent across all walks of society, bringing increased benefits, and increased risks. As society as a whole becomes more dependant on computing, and entire businesses depend on computers for their very existence, entrusting them with their most critical information and tasks, computing has become a trusted cornerstone of business, military and government. This increased reliance on computing has increased interest in trustworthy computing, and several bodies have formed to investigate, formulate and release what they term as “trustworthy computers”. We will be investigating one of these, the Trusted Computing Group , or TCG , and their model for trustworthy computing .
The Trusted Computing Group
The Trusted Computing Group [1] (TCG) is a not-for-profit organisation formed in early 2003 to “ develop, define, and promote open standards for hardware-enabled trusted computing and security technologies, including hardware building blocks and software interfaces, across multiple platforms, peripherals, and devices. [2]” The TCG builds upon an earlier organisation, The Trusted Computing Platform Alliance (TCPA), formed by Intel in 1999[3] as an alliance between several large computing companies, most of whom are now members of the TCG. In fact, nearly all the large names in computing are members of the TCG[4]. The TCPA has recognized the TCG as its successor[5] and contains many of the same member companies, and the terms TCPA and TCG are frequently used interchangeably to refer to one or both of the organisations, the specifications they have released, or even trustworthy computing in general. I will be using TCG to refer only to the Trusted Computing Group, including the TCPA they have largely superseded. The term TC, for trustworthy computing , forms a more apt generalisation of the field, and is the term I shall be using to refer to trustworthy and trusted computing in general.
Trustworthy Computing
The stated purpose of the TCG, and TC in general, is to increase the level of trust we, as computer users, can place in our computers. Both “trust” and “trustworthy” are often misused words, so it is worth clarifying their meaning in the context of TC. [6] explains trust as “ the expectation that a device will behave in a particular manner for a specific purpose. ” Using this definition, we can further say that a trustworthy computer would be a computer that was trusted, and did not betray that trust, and that TC is the field concerned with creating trusted and trustworthy computers.
How TCG works
The TCG has released a non-normative architectural overview[7] giving an outline of the various TCG specifications, their expected use, and some possible implications. [7] explains the basics of how the current TCG specifications would be implemented in both hardware and software, which we will summarise below. It is worth noting that the concepts behind this technology are not new, with several large companies, such as IBM and Microsoft, having their own, often slightly incompatible, implementations. IBM has actually shipped hardware implementations[8] predating both the TCG and the TCPA.
Inherited Trust
The core concept behind the TCG TC model is inherited trust . Perhaps the easiest way to understand this is through an analogy. Assuming I can trust myself, I can then delegate trust to some friend that I trust, and they can in turn delegate trust to a trusted friend of theirs. This works both ways, if someone else trusts me, and I then delegate trust to my friend who in turn passes it on to someone else, we have a chain of trust . The obvious problem with this is that the entire process is vulnerable should the chain of trust be broken at any point – but ignoring this problem for a moment, we can see that there will be a root of trust at some point. Somewhere, there has to be a person who is implicitly trusted, to pass on their trust to the next person, and so forth. This root of trust , and protecting the chain of trust, has been the biggest problem in trust-based computing, and hence the main problem TCG attempts to overcome.
The Trusted Computing Root
The physical aspect of TCG begins with a Trusted Platform Module , or TPM[9], which is typically a hardware device physically attached to a computer in such a manner that it is infeasible to transfer it intact to another computer. This device incorporates several components, which together form a trusted root of computing [10], namely the root of trust for storage (RTS)[11], root of trust for reporting (RTR)[12] and root of trust for measurement (RTM)[13]. Before delving further into the actual workings behind these, let us explore the concepts a little.
The TPM contains, along with the RTS, RTR and RTM, a small portion of non-volatile storage, some platform configuration registers (PCR), a random number generator, and some encryption engines – along with a permanently stored and unique key. Using a typical personal computer as an example[14], when first powered on, the TCM starts and the RTM, which is implicitly trusted, verifies the computer’s basic operating system loading code by storing a digest of the code in the update-only RTS, which in turn verifies the operating system itself, which can then verify an application. This chain of transitive trust [15], which relies on each component verifying the authenticity of the component (or code) above it before passing control to it, with the initial component being implicitly trusted, allows the entire system to vouch that an application is running in a known trusted state – and is the main purpose of TCG. It is important to note that this does not prevent the machine from entering a non-trusted state[16] - it just prevents the machine from lying about its state. What the software chooses to do once it has verified the system as trustworthy is, as we shall see later, quite controversial – but actually outside the scope of the TCG specifications themselves.
Data Integrity
The other major concept that TCG provides for is data binding, signing and sealing[17]. Data binding prevents an encrypted message from being recovered by anyone other than the intended recipient, using standard public-key systems – the major difference being that the keys are stored within the TPM, and hence largely protected from fraud. Data signing is essentially the same as binding, except that it only verifies the authorship and integrity of the data, without encrypting it. Data sealing , which is one of the most powerful features of TCG, takes binding and signing one-step further, and uses the current verifiable state of the machine to encode or sign data, thus verifying that the data was created on a system running in a specified and verifiable state. One of the more controversial aspects of this feature ensures data can only be opened on a specific machine, when it is in a specified state, allowing verifiable platform specific control over data for the first time.
The third major feature of TCG allows for remote attestation – the verifiability of communications between two or more remote entities, using techniques similar to those used for data signing. This feature has caused some serious privacy concerns, as we shall see below.
How TCG Doesn’t Work
TC has caused quite some paranoia, with many opponents claiming sometimes far-fetched and unlikely scenarios[18], often based on incorrect or partial information[19]. Paranoia notwithstanding, TCG does raise some interesting questions and concerns. Many concerns are about privacy , as each TCP ships with a uniquely identifying key. Surprisingly, the TCM is specified as “tamper evident”, not “tamper resistant”, which could be expected to result in private keys being stolen and used by others[20]. To make matters worse, the specification does not provide an efficient method to revoke credentials once they have been issued[20], making key theft a serious identity theft concern.
Privacy
Another concern relates to the top-level key issuing body, known as a certificate authority or CA. To protect the privacy of a TCG platform, a third party CA is trusted to generate identity credentials [21],[22], negating the need to use unique TCM keys directly with other TCM modules. This places a high level of trust in a centralised CA; trust that, if betrayed, could compromise large numbers of TCG platforms, and begs the politically charged question – who will be the top-level CA?
This brings up another issue, where a CA is the only party that knows which private key was used to generate an identity key , but the current TCG specification[16] doesn’t provide a mechanism to prove this, meaning that a CA could potentially fake this information – either proving a connection between a TCM and an identity key that does not exist, or creating an identity key for a TCM that that does not exist[23]. There is no simple solution to privacy concerns such as these, causing some, such as[22], to say that TCG will eliminate privacy entirely.
Economics
A further worry is that TCG, through its ability to prevent access to data except in specific circumstances, could enable certain programs to monopolise specific data. [24] makes the case that this could lead to some programs or companies holding unbreakable monopolies. Perhaps the most controversial aspect of TCG, however, comes about due to its ability to encrypt data in such a way that it can only be decrypted on a machine running in a specific state. Opponents of the concept claim TCG will be used to prevent fair use of various forms of media[25], although this would have to be implemented in software, not directly via TCG.
Conclusion
Having investigated the Trusted Computing Group and their model for trustworthy computing, and discussed the benefits and potential pitfalls inherent in this model, we can conclude that, as computers become increasingly important, the risks associated with a failure of trust will also become increasingly devastating, and thus trustworthy computing will also become ever more imperative. However, whether TCG provides the answers computing needs, is a matter only time will tell. As [26] says,
“Current efforts to secure the PC’s traditionally open architecture will give consumers two unattractive choices: They will either have to pay a huge premium for an unwieldy system that employs impenetrable membranes, encrypted buses, and tamper- resistant memory, or they will have to settle for an inferior solution that fails to thwart dishonest users and limits the ability to backup data and interoperate with third-party software. Investing in proven architectural improvements such as guarded pointers and data tags is a more cost-effective and long-overdue alternative.”
References:
[1] Trusted Computing Group, [Online site], [cited 2004 Aug 23], Available https://www.trustedcomputinggroup.org/
[2] Trusted Computing Group, [Online document], 2004, [Cited 2004 Aug 23], Available https://www.trustedcomputinggroup.org/about/
[3] D. Farber, “Fame, but No Riches, For Cybersecurity,” IEEE SPRECTRUM , Jan, pp 52, 2003
[4] Trusted Computing Group, [Online document], 2004, [Cited 2004 Aug 23], Available https://www.trustedcomputinggroup.org/about/members/
[5] Trusted Computing Group, Backgrounder , 2003, pp 5
[6] Trusted Computing Group, TCG Specification Architecture Overview , Rev 1.2, pp 5, 2004
[7] Trusted Computing Group, TCG Specification Architecture Overview , Rev 1.2, 2004
[8] D. Safford, The Need for TCPA , pp 4, 2002
[9] Trusted Computing Group, Backgrounder , pp 5, 2003
[10] Trusted Computing Group, TCG Specification Architecture Overview , Rev 1.2, pp 19, 2004
[11] Trusted Computing Group, TCG Specification Architecture Overview , Rev 1.2, pp 16, 2004
[12] Trusted Computing Group, TCG Specification Architecture Overview , Rev 1.2, pp 9, 2004
[13] Trusted Computing Group, TCG Specification Architecture Overview , Rev 1.2, pp 24, 2004
[14] Trusted Computing Group, TCG Specification Architecture Overview , Rev 1.2, pp 5, 2004
[15] Trusted Computing Group, TCG Specification Architecture Overview , Rev 1.2, pp 7, 2004
[16] Trusted Computing Group, TCG Main Specification , Ver 1.1b, 2002
[17] Trusted Computing Group, TCG Specification Architecture Overview , Rev 1.2, pp 15, 2004
[18] [Online document], 2004, [Cited 2004 Aug 23], Available http://www.notcpa.org/
[19] [Online document], 2004, [Cited 2004 Aug 23], Available http://www.againsttcpa.com/what-is-tcpa.html
[20] J. Reid, J. M. G. Nieto, E. Dawson, and E. Okamoto , Privacy and Trusted Computing , pp 4,2003
[21] J. Reid, J. M. G. Nieto, E. Dawson, and E. Okamoto , Privacy and Trusted Computing , pp 3,2003,
[22] B. Arbaugh, “Improving the TCPA Specification,” Computer, Aug, pp 78, 2003
[23] J. Reid, J. M. G. Nieto, E. Dawson, and E. Okamoto , Privacy and Trusted Computing , pp 5,2003
[24] E. W. Felten, “Understanding Trusted Computing - Will Its Benefits Outweigh Its Drawbacks?,” IEEE SECURITY & PRIVACY , May/Jun, pp 62, 2003
[25] B. Arbaugh, “Improving the TCPA Specification,” Computer, Aug, pp 78, 2003
[26] B. Arbaugh, “Improving the TCPA Specification,” Computer, Aug, pp 79, 2003
Appendix A – Critical Evaluation of Sources
TCG has proved to be a controversial issue, and as with any controversial issues, the information regarding it ranges from the reputable to the highly disreputable, with many paranoid and misinformed people subverting information for their own purposes. With this in mind, critical judgement of the sources used in this report was very important.
The peer review system usually provides a trusted source of information, providing one affords the peers the liberty of trust and finds them trustworthy. With this in mind, I have attempted to source the majority of my sources from reputable, peer-reviewed sources such as the IEEE database.
I can categorise my sources into two clear types – those that have been through a reputable peer reviewing process, and those that either haven’t, or I can’t verify whether they have or not. Sources such as [1] from the IEEE can be safely assumed to have passed reliable peer reviewing, while sources such as [2] could be expected to have undergone a peer-review process, but this cannot be verified, and one cannot be certain whether the source exhibits any bias towards its employers or not, and as such, one should not implicitly trust such sources.
Sources such as [3] should be treated as suspect, and have mainly been used to show that such opinions, while they have not been peer-reviewed and exhibit, particularly in [4], considerable and unjustified bias, nonetheless do exist.
As an example of the bipolar nature exhibited by varied sources, consider the statement by [5] that:
“The long term result [of TCG] be that it will be impossible to use hardware and software that’s not approved by the [TCG]. Presumably there will be high costs to get this certification and that these would be too much for little and mid-range companies. Therefore open-source and freeware would be condemned to die, because without such a certification the software will simply not work”
In fact, contrast the above with:
“It is worth clarifying that the TCPA specification itself, does not allow a third party to control which operating system and application software a platform owner can run. Therefore, the architecture does not provide a mechanism for software licence enforcement where a platform boot can be terminated by a third party[6]”
As we can see, these two sources are diametrically opposed – only one of the two can actually be correct. In this case, [6] has been through the IEEE peer review process[7], where people who have knowledge of the subject have formally read and referreed the article before it was published. While this doesn’t guarantee the accuracy of the article, it does give it a much higher level of credibility than [3], which has probably not been reviewed by anyone with any credentials or reputation in the field.
Several other critical evaluation techniques[8],[9] were used to evaluate sources, particularly as anyone can publish anything online. With this in mind, for all sources I whether there was a signed author, and if so, who the author was, whether he or she had been referenced by anything else I had read, whether the site was sponsored by, or owned by, a company with a stated interest in the matter and how current the information is. This brings up an interesting question, can we trust sources such as [10] which are from a site which has a stated interest in its own development? I concluded that, as the information was mainly technical and had been through a peer-reviewed system, and that the article is about this information, we could assume that it is an accurate and reliable source.
References:
[1] D. Farber, “Fame, but No Riches, For Cybersecurity,” IEEE SPRECTRUM , Jan, pp 51 2003
[2] D. Safford, The Need for TCPA , 2002
[3] [Online document], 2004, [Cited 2004 Aug 23], Available http://www.notcpa.org/
[4] [Online document], 2004, [Cited 2004 Aug 23], Available http:// www.againsttcpa.com /
[5] [Online document], 2004, [Cited 2004 Aug 23], Available http://www.againsttcpa.com/what-is-tcpa.html
[6] J. Reid, J. M. G. Nieto, E. Dawson, and E. Okamoto , Privacy and Trusted Computing , pp 3,2003
[7] [Online document], 2004, [Cited 2004 Aug 23], Available http://ieeexplore.ieee.org/xpl/Peerreview.jsp
[8] [Online document], 2004, [Cited 2004 Aug 23], Available http://lib.nmsu.edu/instruction/evalcrit.html
[9] [Online document], 2004, [Cited 2004 Aug 23], Available http://www.library.ucla.edu/libraries/college/help/critical/index.htm
[10] Trusted Computing Group, Backgrounder , 2003
My Results
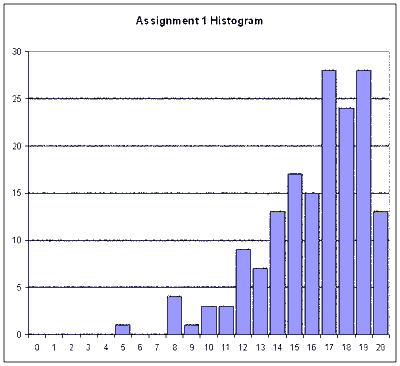
| Assignment 1 | ||
|---|---|---|
| Assets | (out of 4 marks) | 2 |
| Mechanisms | (out of 3 marks) | 3 |
| Social etc | (out of 2 marks) | 1 |
| Sources | (out of 2 marks) | 2 |
| Referencing | (out of 2 marks) | 2 |
| Evaluation | (out of 3 marks) | 3 |
| Criticism | (out of 2 marks) | 2 |
| Structure | (out of 2 marks) | 2 |
| Total | (out of 20 marks) | 17 |
09-SEP-2004